Management of rights models¶
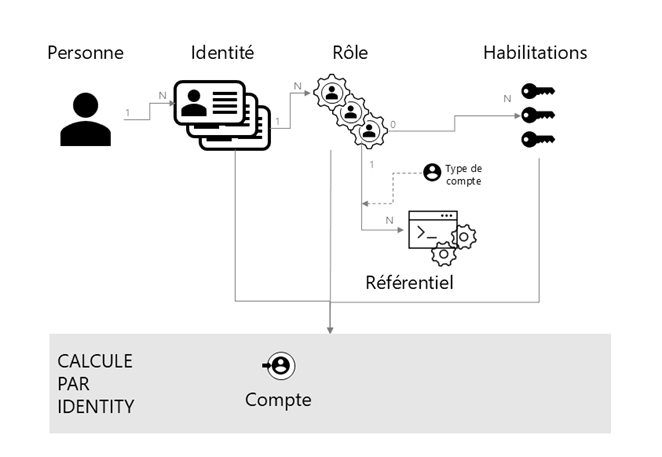
Cyberelements Identity allows you to build access policies based on ABAC (Attribute-Based Access Control), RBAC (Role-Based Access Control), and OrBAC (Organization-Based Access Control) models. Authorization management combines concepts from all three models to enable granular, contextual management of access rights.
The ABAC (Attribute-Based Access Control) model is an access control model that takes into account various attributes and characteristics of users, resources, and the environment to determine access permissions.
The RBAC (Role-Based Access Control) model is an access control model that takes into account the role of users to determine access permissions.
The OrBAC (Organization-Based Access Control) model is an access control model that focuses on structuring permissions based on the organization and its hierarchy. It allows access policies to be defined based on organizational units, positions, and responsibilities within the organization.
With the ability to build access policies by combining the three models, Systancia Identity allows you to manage rights assignment rules by taking into account not only user attributes and roles, but also organizational structures.
For example, a user could have specific authorizations based on their role within the organization, but these authorizations could be modified according to their personal attributes. This allows for a more contextual and granular approach to access rights management, which enhances the security and flexibility of IAM.
With Cyberelements Identity, it is also possible to manage multiple accounts for a single identity.
For example, a person who has a standard role and an application manager role for application A can be assigned two different accounts:
- A standard account for everyday actions
- An admin account for specific solution administration actions