Installation of Mediation Controller servers¶
Note
As a reminder, switching to root on Debian machines must be done with the following command:
1 | |
The instructions given on this page should be replicated on both Mediation Controller servers, starting with the MASTER server first.
When differences appear between the MASTER and SLAVE servers, they will be highlighted. If there is no mention of this, then the instructions apply to both MASTER and SLAVE servers.
Downloading the mirror and necessary tools¶
The cyberelements Cleanroom 4.6 mirror and the Systancia repository signature key can be downloaded from this link (requires the creation of a client account): Systancia Marketplace
In addition to the mirror and key, third-party tools will be required for the upgrade process:
- An SSH client (on Windows, you can use PuTTY)
- An SCP client (on Windows, the WinSCP or FileZilla tools can be used)
Use the SSH client to connect remotely to your server.
Use the SCP client to transfer files to your remote machine.
Preparing for installation¶
Configuration of the network¶
Install the resolvconf package so that the DNS configuration specified in the configuration file that will be modified shortly can be applied:
1 | |
It is essential to configure a static network address for the Mediation Controller. To do this, you first need to retrieve the name of your machine's network interface. Run the following command as root:
1 | |
This command displays the name of the network interface, its status, and the IP addresses assigned to the interface.
??? example “Example” After the command is executed, the following output is displayed:
1 2 3 4 5 | |
Once the network interface name has been obtained, it is now possible to edit the machine's network configuration.
Edit the /etc/network/interfaces file to modify it using the following template:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 | |
Where:
INTERFACE_NAMEmust be replaced by the name of the network interface previously retrieved.RIP_MED_WEB_MASTERmust be replaced by the server's main real IP address, which will be the IP address through which the web consoles can be accessed.NETMASKmust be replaced by the network mask associated with the IP address.NETWORK_GATEWAYmust be replaced by the default network gateway.IP_DNSmust be replaced by the IP address of the DNS server. If several servers need to be configured (3 maximum), separate them with a space.DNS_SUFFIXmust be replaced by the DNS suffix to be used. If no suffix needs to be entered, delete the line.RIP_MED_SSL_MASTERmust be replaced by the secondary real IP address of the server. This will be the IP address through which the SSL Router will be accessible.
??? example “Example”
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 | |
Finally, all that remains is to restart the networking service in order to load the new network configuration:
1 | |
It is essential to configure a static network address for the Mediation Controller. To do this, you first need to retrieve the name of your machine's network interface. Run the following command as root:
1 | |
This command displays the name of the network interface, its status, and the IP addresses assigned to the interface.
??? example “Example” After the command is executed, the following output is displayed:
1 2 3 4 5 | |
Once the network interface name has been obtained, it is now possible to edit the machine's network configuration.
Edit the /etc/network/interfaces file to modify it using the following template:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 | |
Where:
INTERFACE_NAMEmust be replaced by the name of the network interface previously retrieved.RIP_MED_WEB_SLAVEmust be replaced by the server's main real IP address, which will be the IP address through which the web consoles can be accessed.NETMASKmust be replaced by the network mask associated with the IP address.NETWORK_GATEWAYmust be replaced by the default network gateway.IP_DNSmust be replaced by the IP address of the DNS server. If several servers need to be configured (3 maximum), separate them with a space.DNS_SUFFIXmust be replaced by the DNS suffix to be used. If no suffix needs to be entered, delete the line.RIP_MED_SSL_SLAVEmust be replaced by the secondary real IP address of the server. This will be the IP address through which the SSL Router will be accessible.
??? example “Example”
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 | |
Finally, all that remains is to restart the networking service in order to load the new network configuration:
1 | |
One final step remains: modify the machine's internal name resolution so that it resolves its actual primary IP address (corresponding to RIP_MED_WEB_MASTER or RIP_MED_WEB_SLAVE).
To do this, edit the /etc/hosts file and replace 127.0.1.1 with RIP_MED_WEB_MASTER or RIP_MED_WEB_SLAVE depending on the Mediation Controller server.
Example
For a Mediation Controller server whose actual Web IP address is 10.0.10.10 and whose name is mediation-controller.domain.local, the /etc/hosts file will have the following value:
1 2 | |
Attention!
An incorrect configuration of the file may cause an error when installing the collectd package.
Configuring the APT package manager¶
Upload the files downloaded from the Systancia Marketplace to the /tmp/ directory on the server using an SCP client:
systancia.gpgcleanroom-4.6.1-build33.1096.D12-full.tgz
Log in to the server as root, then run the following commands to unzip the Systancia repository, configure its use in APT, and authenticate it.
1 2 3 4 5 | |
We strongly recommend disabling the installation of unnecessary packages when running apt commands. To do so, run the following command:
1 | |
Checking for the presence of the en_US.utf8 locale¶
Installing the Mediation Controller server requires the generation of en_US.utf8 locales.
To check whether they have already been generated on the server, run the following command as root:
1 | |
If the command return displays en_US.utf8 then proceed to the next step of the GRUB configuration.
Otherwise, run the following commands to add this locale to the machine:
1 2 | |
Configuring the GRUB boot program¶
Once these commands have been executed, you must restart the machine after applying a setting in the GRUB boot program:
1 2 3 | |
Installation of the cyberelements Cleanroom Mediation Controller server¶
Installation of basic components¶
Start installing the components using the following command as root:
1 | |
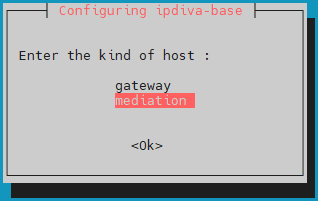
After downloading all dependencies, a window will open asking you to select the server type. Select mediation:
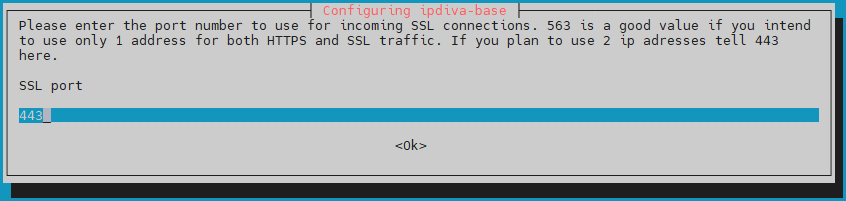
Then you will need to enter the port that the SSL Router will listen on. This listening port is usually set to 443 but the 8443 port can also be used if only one IP is used by the mediation server:
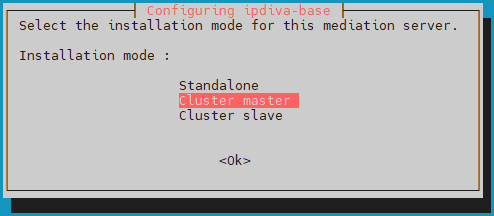
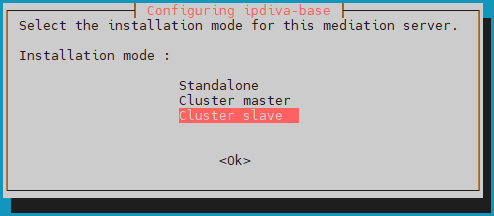
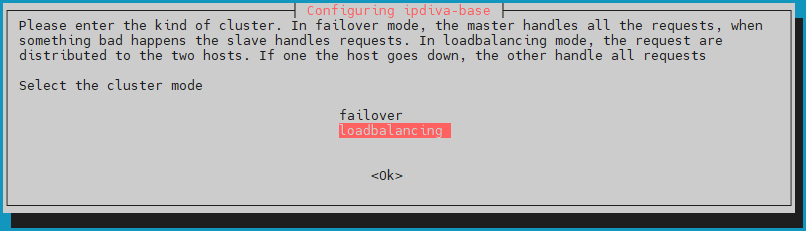
Then set the Cluster mode to loadbalancing so that the user load is distributed across both Mediation Controllers servers:
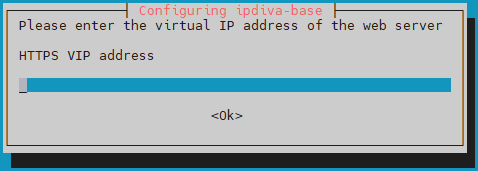
Specify the Web Virtual IP address of the Cluster, VIP_MED_WEB:
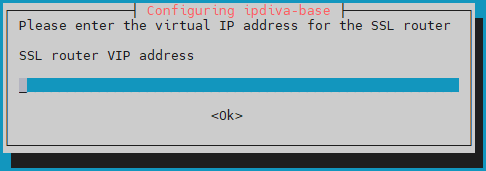
Enter the SSL Virtual IP address of the Cluster, VIP_MED_SSL:
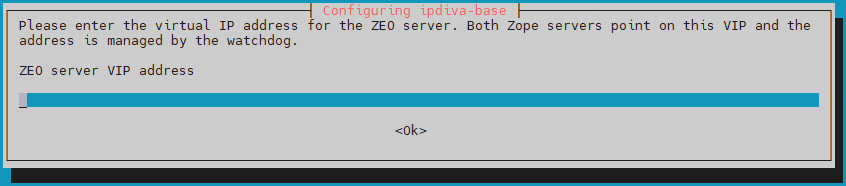
Enter the Virtual IP address of the Cluster configuration database, VIP_MED_ZEO:
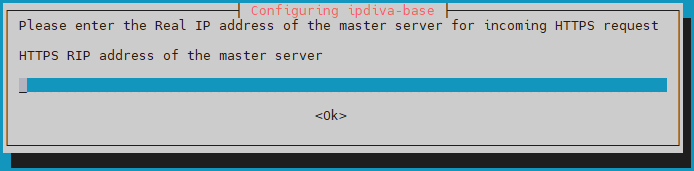
Enter the Web Real IP address of the MASTER Mediation Controller, RIP_MED_WEB_MASTER:
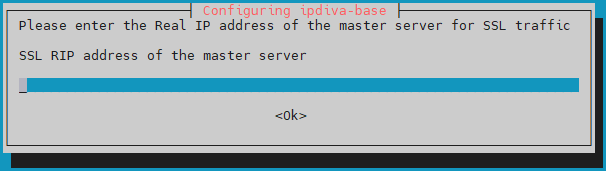
Enter the SSL Real IP address of the MASTER Mediation Controller, RIP_MED_SSL_MASTER:
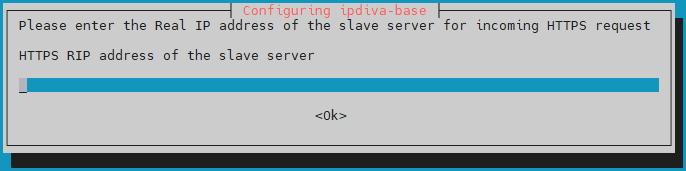
Enter the Web Real IP address of the SLAVE Mediation Controller, RIP_MED_WEB_SLAVE:
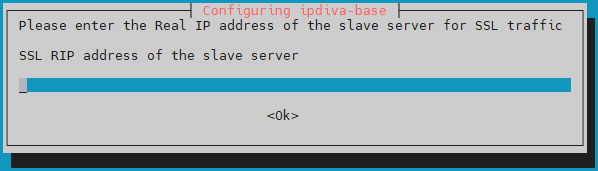
Finally, enter the SSL Real IP address of the SLAVE Mediation Controller, RIP_MED_SSL_SLAVE:
What should I do if there is an error?
If there is an error in the information you entered, continue installing the ipdiva-base package and then use the following command to reconfigure the server:
1 | |
Installation of Cluster Components¶
After installing the basic components, the Cluster components must be installed on the Mediation Controllers servers:
1 | |
After installing the components, a restart is required:
1 | |
Configuration of the Cluster¶
Changing the password of the cyberelements Gate /mediation/system console¶
At this stage of the installation, a new administration interface is available: Change password
Applying licenses and certificates¶
Still in the /mediation/system console, you will need to enter the certificates and licenses for the Mediation Controller server.
Attention!
The SSL Router license and certificate are specific to the MASTER or SLAVE Mediation Controller server.
Configuring the wrong license or certificate will cause malfunctions later on.
Apply the license and certificate for the SSL Router component: 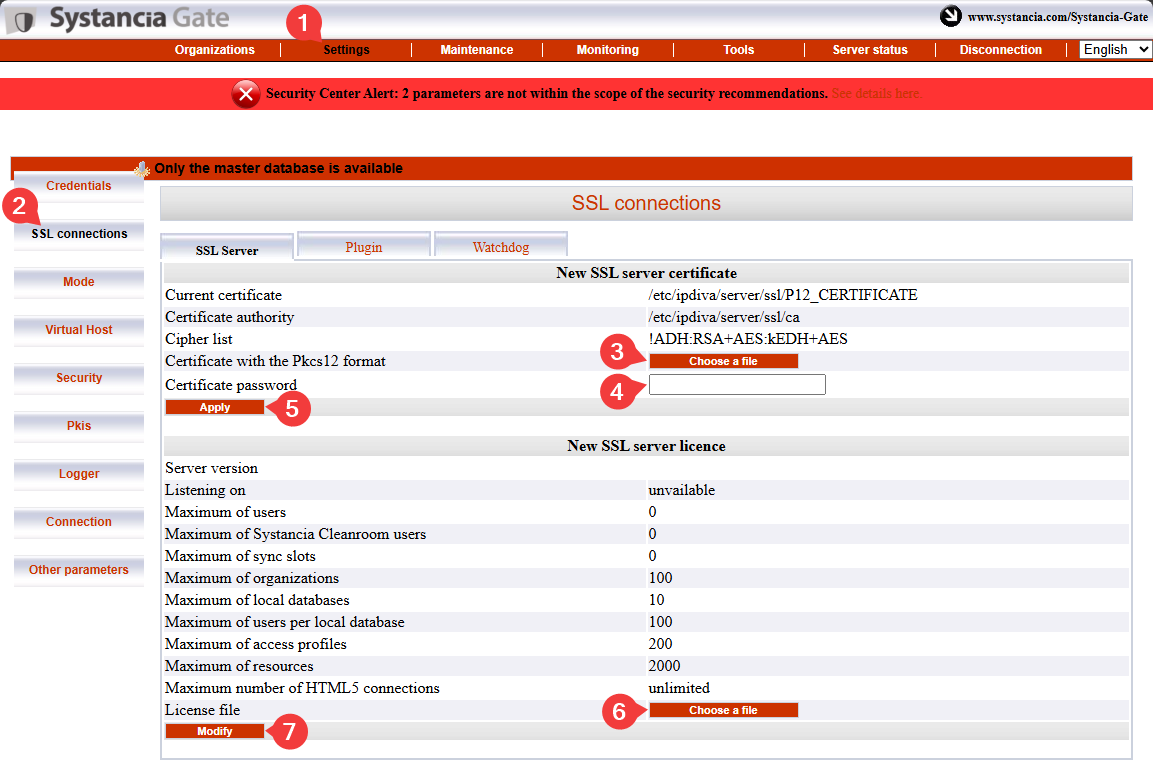
- Click the
Settingstab. - Select
SSL Connectionsfrom the menu. - Search for the certificate for the SSL Router.
- Enter the password for the SSL Router certificate.
- Click
Applyto apply the certificate to the SSL router. - Select the server license file.
- Click
Modifyto apply the server license.
Next, enter the certificate information for the cyberelements Cleanroom client: 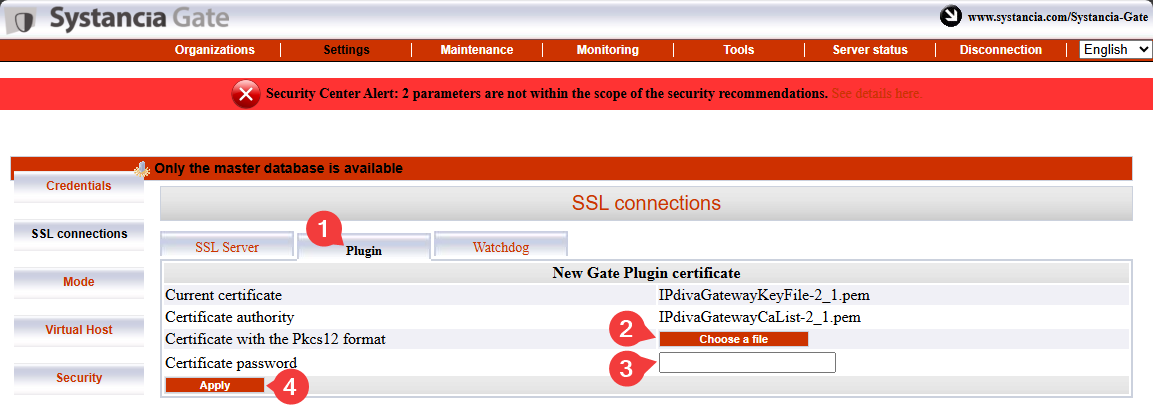
- Select the
Plugintab. - Search for the cyberelements Cleanroom client certificate.
- Enter the certificate password.
- Click
Applyto apply the certificate.
You still need to enter the information for the Watchdog certificate: 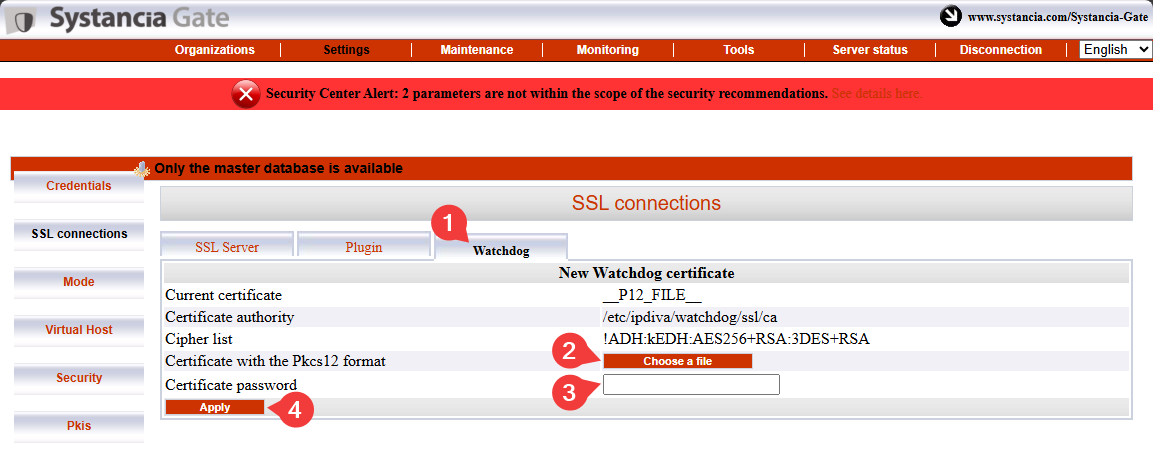
- Select the
Watchdogtab - Search for the Watchdog certificate.
- Enter the certificate password.
- Click
Applyto apply the certificate.
For these changes to take effect, you need to restart the SSL Router and the Watchdog: 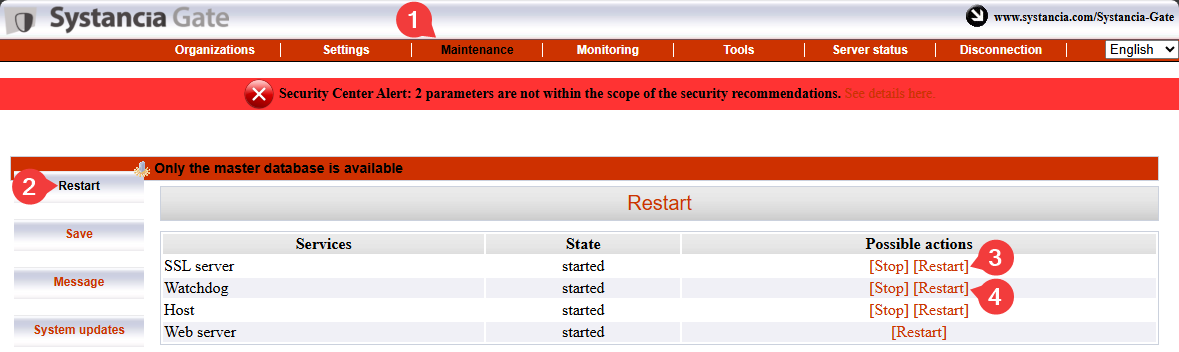
Pairing Mediation Controller servers¶
Attention!
By this point, both Mediation Controller servers must have been configured up to the application of licenses and certificates.
If the SLAVE Mediation Controller server has not yet been configured, please do so by starting from the beginning of this documentation (#installation-of-mediation-controller-servers).
The Mediation Controller server pairing step will establish a trusted link between the two servers and initialize the cluster operation.
On the SLAVE Mediation Controller server
Run the following command as root to initiate a pairing request with the MASTER Mediation Controller server:
1 | |
Replace RIP_MED_WEB_MASTER with the relevant IP address.
??? example “Example”
If RIP_MED_WEB_MASTER is equal to 10.0.10.10, then the command to enter is as follows:
1 2 3 | |
On the MASTER Mediation Controller server
Run the following command as root to check for pending pairing requests and retrieve the request ID:
1 | |
Next, run the following command to accept the pairing request, replacing ID with the ID retrieved from the previous command:
1 | |
??? example “Example”
If the return value of the hostManagerCtl getPendingRequests command is as follows:
1 2 3 4 5 6 7 8 9 10 11 | |
To verify the association, use the following command on the Mediation Controller server (either MASTER or SLAVE):
1 | |
The result will differ depending on the server on which the command is executed:
The expected result on the MASTER Mediation Controller server is as follows:
1 | |
??? example “Example”
1 | |
The expected result on the SLAVE Mediation Controller server is as follows:
1 | |
??? example “Example”
1 | |
On the SLAVE Mediation Controller server
You can check the bootstrap status from the SLAVE server using the following command:
1 | |
A cluster that is not experiencing any synchronization issues will return the value 0.
A final series of commands is required, again on the SLAVE server, to synchronize a secret shared between both Mediation Controllers:
1 2 | |
Activation of the interserver link¶
What is the purpose of the inter-server connection?
This is a special connection for cluster operation that allows a Mediation Controller server to route traffic to another Mediation Controller server in cases where the target Edge Gateway is not connected to the first server but only to the second.
For example, if the MASTER Mediation Controller server is no longer connected to the Edge Gateway, it can use the interserver link to reach the Edge Gateway via the SLAVE Mediation Controller server.
flowchart LR
MASTER(Mediation Controller<br/>MASTER) --x |Connection lost| GW(Edge Gateway)
MASTER --> |Interserver link| SLAVE(Mediation Controller<br/>SLAVE) --> GWOn the MASTER Mediation Controller server
Edit the /etc/ipdiva/server/remoteServers.xml file to indicate the CN of the interserver certificate:
1 2 3 4 5 6 7 8 9 | |
Replace SLAVECN with the CN of the certificate intended for the interserver connection.
If you do not know the CN of the interserver certificate, then the character * can be entered (u recommended if in doubt):
1 2 3 4 5 6 7 8 9 | |
??? example “Example” Taking into account the following information:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 | |
On the SLAVE Mediation Controller server
Send the interserver certificate to the SLAVE Mediation Controller in the /tmp/ directory.
Next, run the following commands as root to move it to the target directory with the appropriate permissions:
1 2 3 | |
Next, edit the /etc/ipdiva/server/remoteServers.xml file to add the following content to the <remoteConfig> tag (the old <localCluster> tag can be deleted entirely):
5 6 7 8 9 10 11 12 13 14 15 16 17 | |
Replace:
MASTERCN: specify the CN of the SSL Router certificate of theMASTERMediation Controller, which is usuallyRIP_MED_SSL_MASTER.RIP_MED_SSL_MASTER: corresponds to the secondary IP address of theMASTERMediation Controller.PORT_RIP_MED_SSL_MASTER: this is the port listened to by the SSL router of theMASTERMediation Controller; it is usually443.INTERSERVER.P12: name of the certificate intended for the interserver.PASSWORD: interserver certificate password.
??? example “Example” Taking into account the following information:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 | |
Modify the configuration of the SLAVE SSL router by running the following command:
1 | |
On the MASTER and SLAVE Mediation Controller servers
Restart the SSL Router to apply the interserver link settings:
1 | |
To confirm that the interserver link is working properly, the following command should return a result:
1 | |
The previous command should produce a log containing the following: TRACE Router.floodWithLocalInfos sent 0 peer(s), 0 foreignPeers, and 0 multicast group(s).
If no such log is displayed, check the configuration set up in this chapter.
In the /mediation/system web console of the MASTER Mediation Controller
Enable the inter-server connection between the two Mediation Controllers by editing the default SSL virtual host: 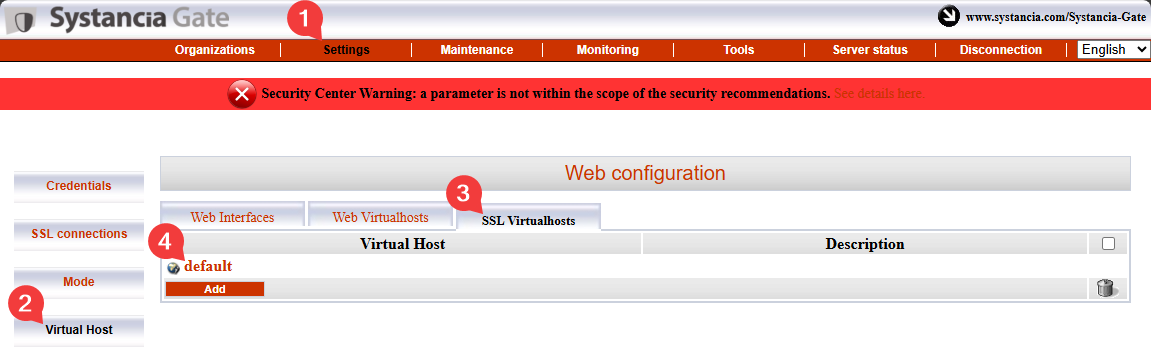
Fill in the various fields using the instructions below and enable the cross-server linking feature by checking the box labeled Is cross-server linking configured?: 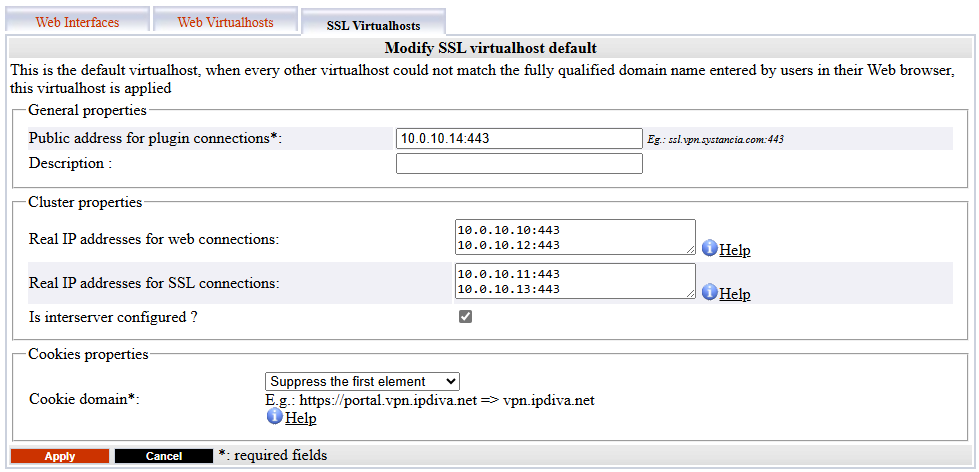
Public address for plugin connections: corresponds toVIP_MED_SSLfollowed by its listening port (usually443).Actual public IP addresses for web connections: corresponds to the pair of actual web IP addresses (RIP_MED_WEB_MASTERandRIP_MED_WEB_SLAVE) with their corresponding ports, one line per IP address and port pair.Actual public IP addresses for SSL connections: corresponds to the actual SSL IP address pair (RIP_MED_SSL_MASTERandRIP_MED_SSL_SLAVE) with their corresponding ports, one line per IP address and port pair.
Installation of specific cyberelements Cleanroom components¶
Start installing cyberelements Cleanroom components on Mediation Controllers servers using the following command:
1 | |
The servers must be restarted to complete the installation:
1 | |
Connecting to the PostgreSQL database¶
To function, cyberelements Cleanroom requires the use of an external PostgreSQL database (DB) to store its settings and various logs in the /system console.
If the DB is directly accessible from the Mediation Controller servers, proceed directly to the DB initialization step.
Connecting to a database on the LAN¶
In order to enable connection to a database located on the LAN without opening a DMZ to LAN flow, the database flow will be redirected through a TLS tunnel between the Edge Gateways and the Mediation Controllers.
To achieve this, it is necessary to configure one Edge Gateway (or two Edge Gateways) using the underlying cyberelements Gate technology.
Declaration of cyberelements Gate Edge Gateways¶
To do this, start by logging in to the /mediation/system console in cyberelements Gate.
Then go to the “Organizations” menu and click “Add”: 
Enter the organization name, which must be different from the one assigned to cyberelements Cleanroom (for example, tunnel), and specify at least one user session license along with the password for the admin account: 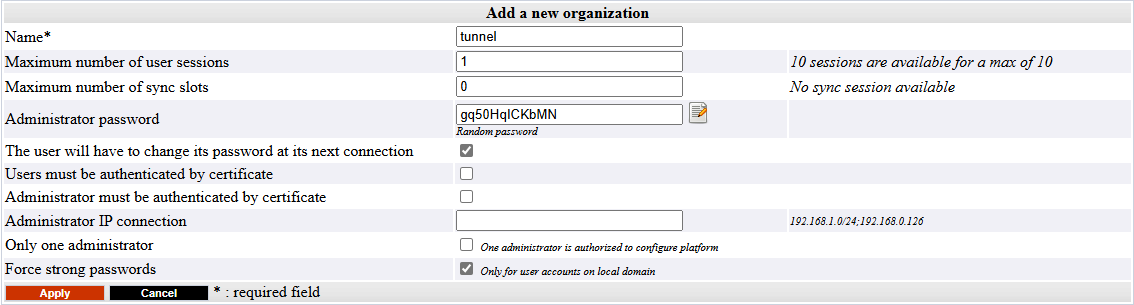
Log in to the administration interface of the organization you created earlier using the admin account by going to /gate/admin: 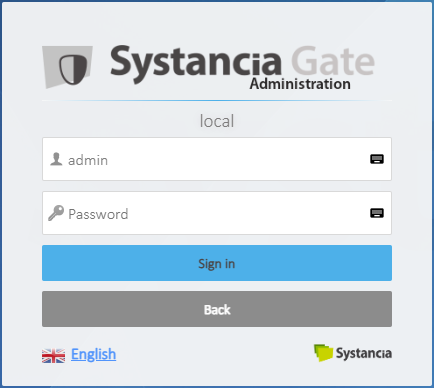
Then declare both Edge Gateways that will be used to set up the tunnel.
On the left, hover over Infrastructure, click Gateways, and then click the Add button: 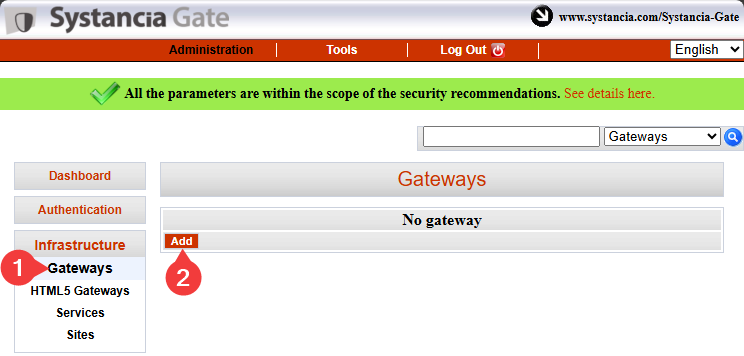
Enter the name of the first Edge Gateway and confirm the entry: 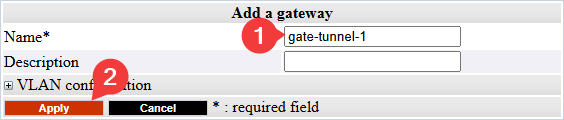
Information
As a reminder, the name of an Edge Gateway is linked to the certificate it will use to authenticate itself with the SSL Router of the Mediation Controller.
This name takes the following form <GW_NAME>@<ORGANIZATION_NAME>, where <GW_NAME> corresponds to the name of the Edge Gateway and where <ORGANIZATION_NAME> corresponds to the organization name created in the cyberelements Gate system console.
Repeat the Edge Gateway declaration step for the second Edge Gateway.
Tunnel connections and settings on Edge Gateways¶
Information
The following steps can be replicated on both Edge Gateways used for the tunnel to access the database.
!!! warning “Prerequisites” To complete this part, you will need to use either:
1 2 | |
First, use a tool such as WinSCP or FileZilla to transfer the certificate required for the connection to the /tmp/ directory on the Edge Gateway via SCP.
Then connect via SSH and switch to root.
To connect the Edge Gateway to both Mediation Controllers, you need to create two new Edge Gateway instances: one will connect to the MASTER Mediation Controller, while the other will connect to the SLAVE Mediation Controller.
To create them, run the following commands:
1 2 | |
Copy the certificate file to the /etc/ipdiva/gateway-tunnel-master/ssl/ and /etc/ipdiva/gateway-tunnel-slave/ssl/ directories:
1 2 | |
Replace <CERT_NAME> with the name of the certificate that the Edge Gateway must use to connect to the Mediation Controller.
Configure the Edge Gateway instances to allow them to connect to the Mediation Controllers.
The configurations differ depending on the Mediation Controller to be contacted. Perform both settings:
Edit the file /etc/ipdiva/gateway-tunnel-master/gateway.xml and complete it using the following information (several sections have been omitted and are indicated by […]):
1 2 3 4 5 6 7 8 9 10 11 12 | |
Replace the following elements:
@SERVER@: must be replaced with theRIP_MED_SSL_MASTERaddress@SERVERPORT@: must be replaced with the SSL router's listening port, normally set to443keyfile.pem: must be replaced with the name of the certificate filePASSWORD: must be replaced with the certificate password@RPC_PORT@: must be replaced with a port that is not currently listening on the machine; port9082can be used
??? example “Example” Taking into account the following information:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 | |
Edit the file /etc/ipdiva/gateway-tunnel-slave/gateway.xml and complete it using the following information (several sections have been omitted and are indicated by […]):
1 2 3 4 5 6 7 8 9 10 11 12 | |
Replace the following elements:
@SERVER@: must be replaced with the addressRIP_MED_SSL_SLAVE@SERVERPORT@: must be replaced with the SSL router's listening port, normally set to443keyfile.pem: must be replaced with the name of the certificate filePASSWORD: must be replaced with the certificate password@RPC_PORT@: must be replaced with a port that is not currently in use on the machine; port9083can be used
??? example “Example” Taking into account the following information:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 | |
Now that the instances are configured to connect to the Mediation Controllers, they still need to be configured to redirect the Mediation Controller connection to the database.
To do this, edit the /etc/ipdiva/gateway-tunnel-master/services.xml file and modify it as follows:
1 2 3 4 5 6 7 8 9 | |
Replace DB_SERVER with the DNS name or IP address used to connect to the database, and DB_PORT with the listening port of the database instance.
Replicate these settings for the instance connecting to the SLAVE Mediation Controller server by copying the file:
1 | |
Finally, start the Edge Gateway instances so that they establish a connection to the Mediation Controllers:
1 2 | |
Configuring the Mediation Controllers tunnel¶
In order for the tunnel to be usable by the Mediation Controllers, you still need to declare their existence.
To do this, log in as root to the Mediation Controllers and edit the /etc/ipdiva/server/services.xml file to add the following section (several sections have been omitted and are marked with […]):
1 2 3 4 5 6 7 8 9 10 11 12 13 14 | |
Replace the following elements:
GW1_NAMEby the name of the first Edge GatewayGW2_NAMEby the name of the second Edge GatewayORGANIZATION_NAMEby the name of the cyberelements Gate organization that was created previously
??? example “Example” Taking into account the following information:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 | |
To apply the new configuration, restart the SSL Router with the following command:
1 | |
Initializing the database¶
Attention!
You must create the default database before cyberelements Cleanroom initializes it (it is not created automatically).
To initialize the PostgreSQL system configuration database, you must first configure the connection settings on the Mediation Controllers.
To do this, edit the /etc/ipdiva/care/databasesettings.ini file on both servers and add the following entries:
2 3 4 5 6 7 8 9 | |
Replace the following elements:
DB_USERNAMEby the username used to connect to the database.DB_PWDby the password of the user logging in.DB_HOSTby the IP address or DNS name used to connect to the database; if a connection via Edge Gateways is used, then you will need to enter127.0.0.1.DB_PORTby the port used to connect to the database instance; if a connection via Edge Gateways is used, then you will need to enter1432.
The database initialization can be launched with the following commands, to be executed only on a Mediation Controller:
1 2 | |
After that, all that remains is to restart the apache2 service on both Mediation Controllers to apply the initialization of the system database:
1 | |
Installation of drivers for connecting to Microsoft SQL databases¶
If you want to connect to an external database and it is a Microsoft SQL Server, then additional ODBC drivers must be installed.
Two versions are available: version 17 and version 18.
TLS connection required for drivers in version 18
Using ODBC 18 drivers requires that the connection be encrypted using TLS. To do this, you need to configure MS SQL Server for connection encryption.
Before starting the installation of ODBC drivers, you must install the necessary packages for preparation, then prepare the Microsoft repository for the package installation:
1 2 3 4 | |
Next, install the drivers according to the selected version and configure the system to use the sqlcmd command:
1 2 3 | |
1 2 3 | |
The ODBC drivers are now correctly installed.
If the Mediation Controller server has access to an MS SQL server, the following command should allow the connection to the remote server:
1 | |
Where:
SERVERshould be replaced with the DNS name or IP address of the MS SQL server.INSTANCE_NAMEshould be replaced with the name of the instance to connect to; if not necessary, also remove the \ character.PORTshould be replaced with the connection port to the MS SQL database instance.USERshould be replaced with the username for establishing the connection.
Examples
If the Mediation Controller server has access to an MS SQL database server via the IP address 10.0.10.100, the instance to be accessed is listening on the port 1433, and the access account is sql-user. Then the connection command is as follows:
1 | |
If the connection instance named MSSQLINSTANCE had to be specified, the command would be modified as follows:
1 | |
Configuring an NTP time server¶
It is recommended to set up a time server to keep the system clock up to date. The necessary steps are described on the NTP configuration page.
Initial configurations on cyberelements Cleanroom¶
Authorization of access to web interfaces with the virtual IP¶
By default, it is not allowed to connect to the product's cyberelements Cleanroom web interfaces with the virtual IP VIP_MED_WEB.
To add the authorization, run as root the following commands on the Mediation Controllers:
1 2 | |
Replace IP with the IP address corresponding to VIP_MED_WEB.
Initial configurations¶
At this stage, the Mediation Controllers servers are installed, but several actions still need to be performed:
-
Change the default passwords
Change the default passwords for the system consoles.
-
Install certificates and licenses
The Mediation Controller requires various certificates and a license to be operational.
Only the certificate for the cyberelements Cleanroom client needs to be re-declared on both Mediations Controllers (use the RIPRIP_MED_WEB_MASTERandRIP_MED_WEB_SLAVE). -
Configure the web certificate
Configure the web certificate used to connect to web interfaces
-
Declare a DNS name
Add a DNS name authorized to connect to web interfaces.
-
Configure the organization
Configure the cyberelements Cleanroom organization.
Configure with direct access to the database
Configure with access to the database via the Edges Gateways tunnel
-
Declare the Edge Gateways
Declare the Edge Gateway(s) or HTML5 Gateway(s) to be installed.
-
Create a logical site
Create and configure a logical site that groups together Edge Gateways and HTML5 Gateways that can access local resources.
-
Install an Edge Gateway
Install and configure a new Edge Gateway with the newly installed Mediation Controller servers.
An HTML5 Gateway instance will also be configured.